TLS 1.2 for QuickBooks Desktop for Windows
by Intuit•3• Updated 10 months ago
Learn what the system requirements are to run TLS 1.2 security protocol on your computer for QuickBooks Desktop 2018 and later.
To get the best experience in QuickBooks, make sure you’re using TLS 1.2. We'll tell you about it and how it affects system requirements for QuickBooks Desktop.
What is TLS 1.2?
TLS 1.2 is an Internet security protocol that’s quickly becoming an industry security standard. To provide greater security and stability, all connections used by QuickBooks Desktop to access Intuit services need to meet certain system requirements. If not met, affected services may include the following:
- All connected services such as payroll, payments, and online banking.
- QuickBooks Desktop activation on a new computer
- Password reset tool
- Services that require Intuit account credentials like My apps, secure webmail, and contributed reports.
- Intuit Data Protect (IDP)
- Help pages
- Ordering checks and supplies
- VAT e-filing
The TLS 1.2 Readiness tool updates your system to become TLS 1.2 compliant as long as it meets all Windows Operating System, Internet Explorer and .Net requirements.
System requirements
To prevent any issues with these services and others, make sure to update your QuickBooks to meet these requirements:
Operating System
- Windows 10
- Windows Server 2008 R2
- Windows Server 2012 R2
- Windows Server 2017
Important: Here's what you need to know if you're still in Windows 7 or Windows 8.1.
Internet Explorer
QuickBooks Desktop uses features of Internet Explorer. Make sure that you install Internet Explorer 11 to have the latest updates from Microsoft.
- Close QuickBooks Desktop.
- Update to IE 11.
- Reopen QuickBooks Desktop.
.Net framework
QuickBooks needs version 4.5.2 or greater of .NET framework. Here’s how you can get it up-to-date.
- Download .NET Framework from Microsoft's website.
- Save the file to your desktop.
- Double-click the file and follow the on-screen instructions.
- Reboot your computer after the installation.
Note: If you encounter any errors while installing .NET framework, contact an IT professional or Microsoft.
Internet Explorer Group Policy
If you see an error message, you may need to talk to your IT person or department to allow TLS 1.2 protocol in Internet Explorer.
If the Internet Explorer Group Policy shows that you have the correct IE but TLS 1.2 still needs further set up, follow this Microsoft article.
Elevated privileges
If you see an error message, you may need to run QuickBooks with elevated privileges, which establishes correct Internet security settings.
- Close QuickBooks.
- Right-click the QuickBooks icon.
- Select Run as Administrator.
Solution: Run the TLS 1.2 Readiness tool from the QuickBooks Tool Hub
When you run this tool, you'll update your operating system to be TLS 1.2 compliant.
Step 1: Download and install the QuickBooks Tool Hub
The QuickBooks Tool Hub helps fix common errors. You'll need to close QuickBooks to use the tool hub. For the best experience, we recommend you use Tool Hub on Windows 10, 64-bit.
- Close QuickBooks.
- Download the most recent version (1.6.0.5) of the QuickBooks Tool Hub. Save the file somewhere you can easily find it (like your Downloads folder or your Windows desktop). Note: If you've installed Tool Hub before, you can find out which version you have. Select the Home tab. The version will be on the bottom.
- Open the file you downloaded (QuickBooksToolHub.exe).
- Follow the on-screen steps to install and agree to the terms and conditions.
- When the install finishes, double-click the icon on your Windows desktop to open the tool hub.
![]()
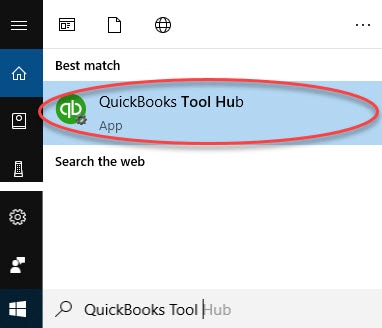
Note: If you can't find the icon, do a search in Windows for QuickBooks Tool Hub and select the program.
Step 2: From the Tool Hub, run the TLS 1.2 tool
- In the QuickBooks Tool Hub, Select Installation Issues.
- Select QuickBooks TLS 1.2 Tool from the bottom right corner.
- Select OK to open the TLS Tool and then Yes to the EULA Agreement.
- Select Run.
- Once the tool competes, select Exit.
You must sign in to vote.
Sign in now for personalized help
See articles customized for your product and join our large community of QuickBooks users.
Find the right fit for your business
![[object Object]](https://digitalasset.intuit.com/content/dam/intuit/sbsegcs/en_us/quickbooks-online/images/SDR-qbo-rightrail.png)
Choose from plans and features to fit your business needs with QuickBooks Online.
More like this
- Error 15223by QuickBooks
- Fix internet connection problems in QuickBooks Paymentsby QuickBooks
- System requirements for QuickBooks Desktop 2021by QuickBooks
- System requirements for QuickBooks Desktop 2024by QuickBooks